When a computer application violates the basic principles of software setup and functioning, one of which is the user’s authorization, it is hard to classify as legitimate. This is why the browser hijacker Qtipr.com is labeled as adware.
The underlying reasons in this case are, first of all, the installation which is close to drive-by, and the unapproved changes that the app makes to the browser preferences on the infected system.
As per a somewhat closer analysis, this digital parasite appears to be related to the site hosted at Qtipr.com. That’s the place on the web hosting the entire advertising platform that the unwanted ads are backed by. Also, it’s the page the affected users are redirected to when they click the Ad Options button on the adverts. Interestingly, you cannot always visit that site – the browser comes up with a blank page.
How does this complex scheme actually work and help the bad guys benefit from it? At the beginning, there is always a barely noticeable installation of the Qtipr.com malicious browser helper object. Most of the time the trespassing process is assisted by free third party programs that bundle the adverse item in their installation. The idea is to make the presence of the extra object as inconspicuous as possible, so the default setup of affiliated utilities already has the payload in it. The criminals are well aware that users aren’t keen on reading that kind of stuff, leaving the recommended options as they are. This lack of caution eventually leads to contamination.
When the Qtipr.com virus is inside the machine, it displays interstitial ads, pop-ups, coupons, freebies, price comparisons and links embedded into keywords on the pages the victim visits. There are loads of these things on all sites, not only the ones related to ecommerce. It takes some bandwidth to load the ads, so the user has a hard time opening pages. Also, seeing the actual content on sites becomes a challenge because Ads by Qtipr.com are definitely redundant. Beyond all doubt, this sort of app does not belong on a healthy computer, so it should be removed using tailor-made instructions.
Automatic removal of Qtipr.com infection
The benefits of using the automatic security suite to get rid of this infection are obvious: it scans the entire system and detects all potential fragments of the virus, so you are a few mouse clicks away from a complete fix.
- Download and install recommended malware security suite
- Select Start Computer Scan feature and wait until the utility comes up with the scan report. Proceed by clicking on the Fix Threats button, which will trigger a thorough removal process to address all the malware issues compromising your computer and your privacy.
Get rid of Qtipr.com using Windows native uninstall feature
- Select Control Panel entry in the Windows Start menu. Go to Programs and Features (Windows 8), Uninstall a program (Windows Vista / Windows 7) or Add or Remove Programs (Windows XP)
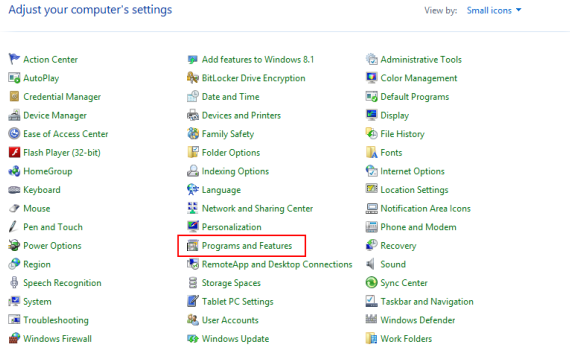
- On the Uninstall or change a program screen, find the entry for Qtipr.com or any similar-looking new application. Select it and click Uninstall/Change
- Be advised this technique works well for the regular applications but might be inefficient for removing malicious programs.
Remove Qtipr.com virus from web browser
The workflow below is intended to eliminate malicious objects, such as add-ons or plugins, from the browsers that got impacted. Given the persistence-related features of this particular infection, the optimal workaround is to restore the affected browser’s settings to their original state. This will prevent the virus from further interfering with your preferences.
Qtipr.com removal from Google Chrome
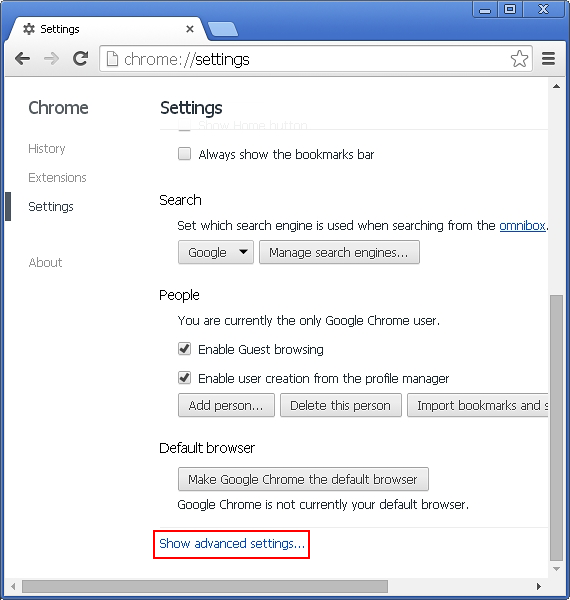
- Click the Chrome menu icon and select Settings
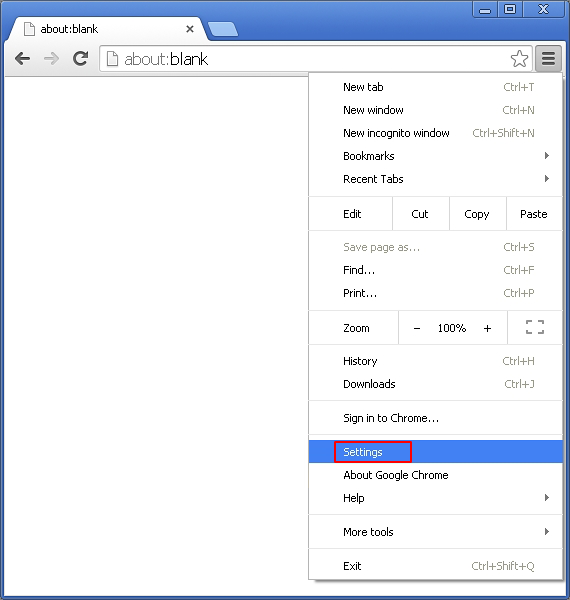
- When the Settings screen opens, find the link that says Show advanced settings and click on it
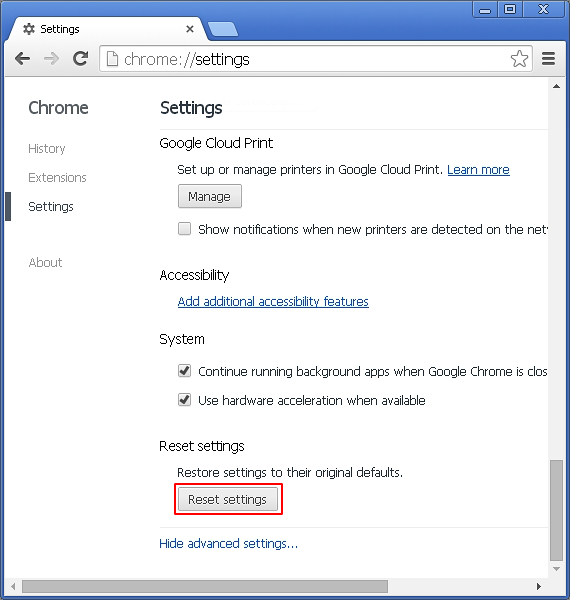
- Proceed by clicking on the Reset browser settings button
- For you to evade any unintended consequences of the reset, Chrome will display a note about the settings and fragments of browsing data that will be lost. Read the notification and click Reset in case you agree
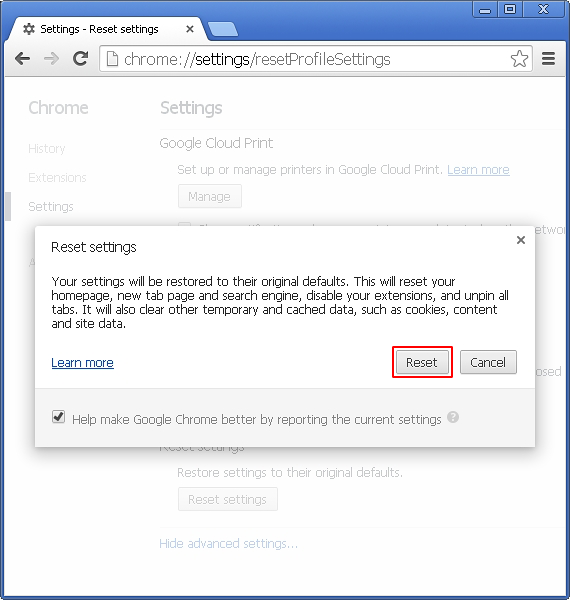
- Restart Chrome.
Qtipr.com removal from Mozilla Firefox
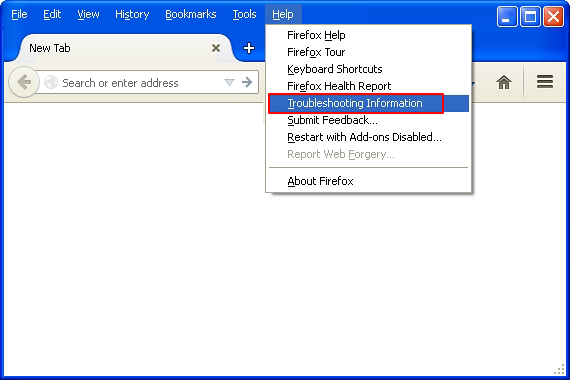
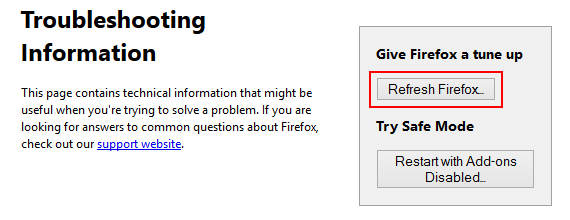
- Open Firefox and select Troubleshooting Information on the Help drop-down list
- Locate the sub-section titled Give Firefox a tune up and click on the Refresh Firefox button to proceed. Then confirm the transaction on the respective popup
- Restart Firefox.
Qtipr.com removal from MS Internet Explorer
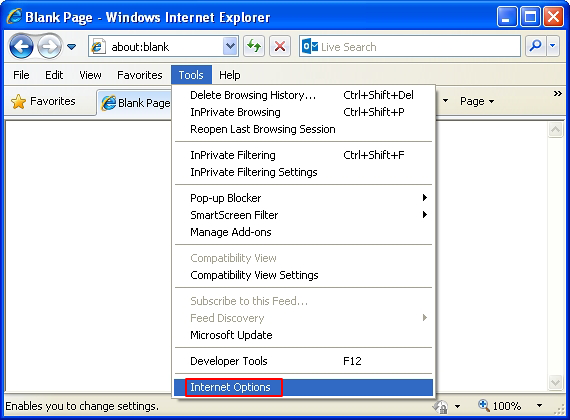
- Select Internet Options under Tools in IE
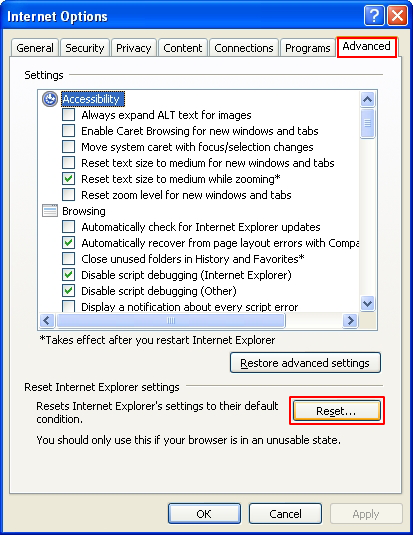
- Select the Advanced tab on Internet Options screen and click on the Reset button
- The browser will now display the Reset Internet Explorer Settings dialog. Review the points on what the resetting includes. Activate the option saying Delete personal settings and click on the Reset button as shown on the image
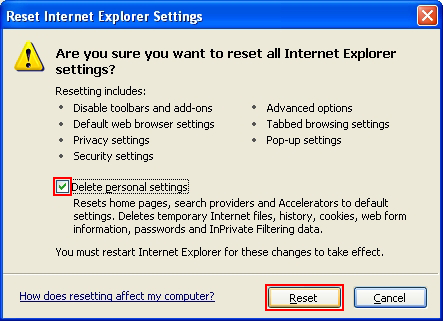
- Restart the computer
Verify thoroughness of the removal
Having carried out the instructions above, add a finishing touch to the security procedure by running an additional computer scan to check for residual malware activity.