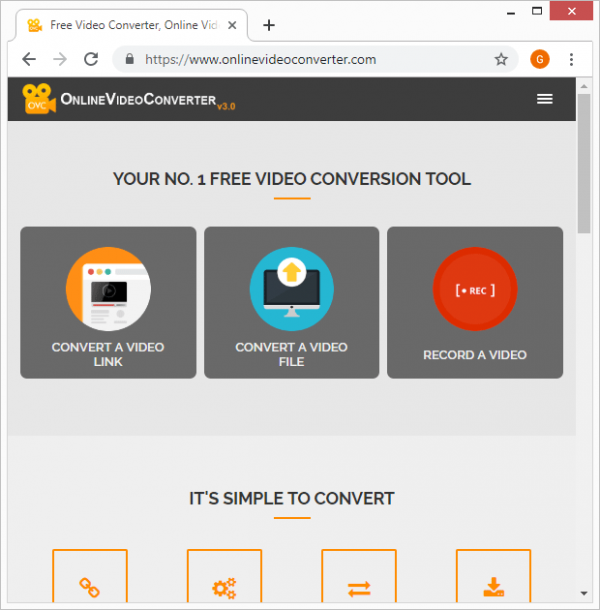
Although Internet connectivity is the ubiquitous norm nowadays, users may need to download multimedia content onto their devices rather than watch streaming videos. The common motivation for doing so is to be able to enjoy a favorite clip or movie when offline. There are tools that do or claim to do the conversion trick in this scenario. OnlineVideoConverter is one of them, being marketed as a free utility that allows you to simply enter a hyperlink of a video on a source like YouTube, Instagram, or Facebook and download it. By the way, grabbing video materials from some of these sources is a slippery slope and can even be illegal. The program in question also purports to convert a media file that’s already on a device or cloud storage into a different format. This sure sounds great, but there are serious pitfalls regarding this service.
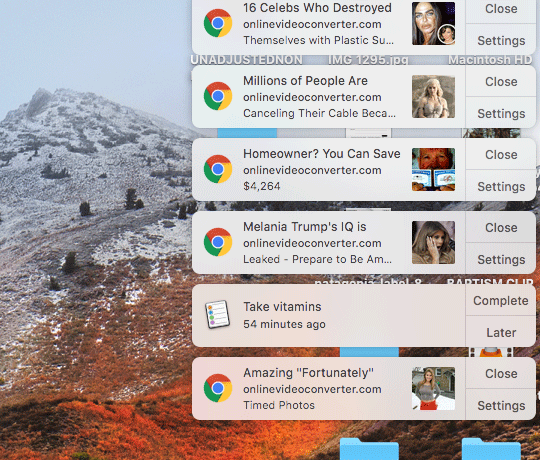
When you opt for the perks offered by OnlineVideoConverter, there could be some shady activity going on behind the scenes. While the tool may actually handle and transform the content as promised, it requires certain permissions in the web browser. The problem is that there are no clear requests being generated along the way, which means the app obtains privileges in an unauthorized fashion. Among other things, it abuses the “Notifications” framework. Regular websites may leverage this system for benign purposes, such as to inform the visitors about important updates a breaking news. However, OnlineVideoConverter extends this functionality for a peculiar objective, which comes down to triggering nag screens and obtrusive ads. As a result, the victim’s browsing experience will be interrupted by sponsored links that appear within popup ads. Not only do these annoying advertisements show up in the user’s preferred web browser, but they will also occur in the background as long as the Internet navigation software is running.
Despite the fact that the popup ads say “onlinevideoconverter.com”, they redirect the victim to a different site whenever clicked on. This predicament resembles a garden-variety adware attack that entails hugely obnoxious malvertising activity the user cannot easily stop. To top it off, there is another malicious facet of this virus. It is known to additionally promote PUPs (potentially unwanted programs) or even outright malware. In pursuit of monetizing their “free” service to a maximum, the authors of OnlineVideoConverter appear to engage in a multi-pronged stratagem that leads to ads being triggered and drive-by downloads going off behind the victim’s back.
As if this weren’t enough, the infection also harvests private browsing data when operating on a device. It may specifically zero in on the user’s web surfing history, bookmarked pages, and authentication details such as usernames and passwords. It goes without saying that such an encroachment on privacy is a dangerous encounter. Ultimately, the only reasonable approach in dealing with OnlineVideoConverter virus is to wipe it off of the compromised system. Scroll down this page to learn how the repair should be implemented.
Automatic removal of OnlineVideoConverter infection
The benefits of using the automatic security suite to get rid of this infection are obvious: it scans the entire system and detects all potential fragments of the virus, so you are a few mouse clicks away from a complete fix.
- Download and install recommended malware security suite
- Select Start Computer Scan feature and wait until the utility comes up with the scan report. Proceed by clicking on the Fix Threats button, which will trigger a thorough removal process to address all the malware issues compromising your computer and your privacy.
Remove OnlineVideoConverter virus using Windows native uninstall feature
- Select Control Panel entry in the Windows Start menu. Go to Programs and Features (Windows 8), Uninstall a program (Windows Vista / Windows 7) or Add or Remove Programs (Windows XP)
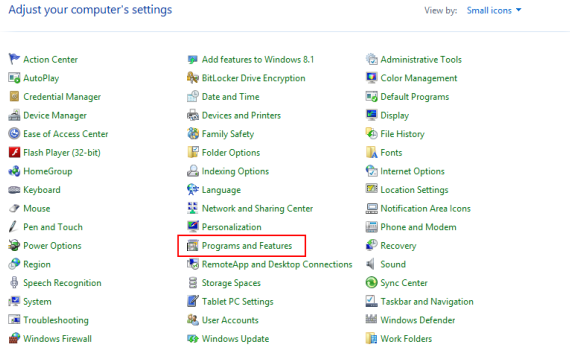
- On the Uninstall or change a program screen, find the entry for OnlineVideoConverter or any similar-looking new application. Select it and click Uninstall/Change
- Be advised this technique works well for the regular applications but might be inefficient for removing malicious programs.
Remove OnlineVideoConverter virus from web browser
The workflow below is intended to eliminate malicious objects, such as add-ons or plugins, from the browsers that got impacted. Given the persistence-related features of this particular infection, the optimal workaround is to restore the affected browser’s settings to their original state. This will prevent the virus from further interfering with your preferences.
OnlineVideoConverter ads removal from Google Chrome
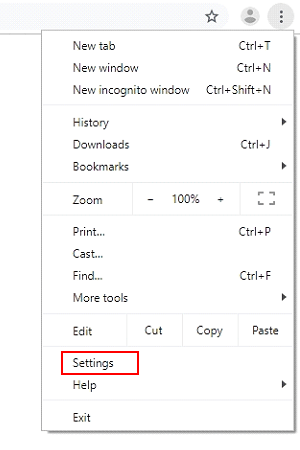
- Click the Customize and control Google Chrome icon and select Settings
- When the Settings screen opens, find the link that says Advanced and click on it
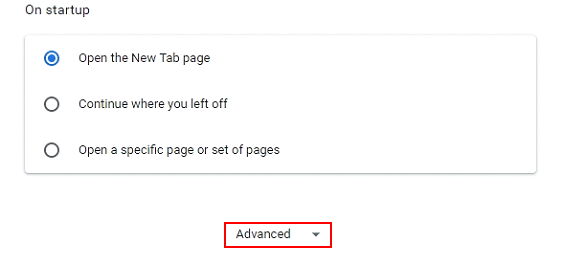
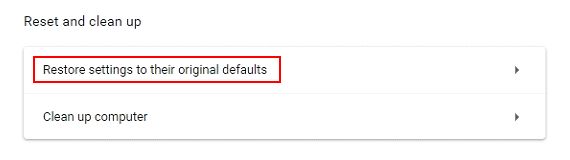
- Proceed by clicking on the Restore settings to their original defaults button
- For you to evade any unintended consequences of the reset, Chrome will display a note about the settings and fragments of browsing data that will be lost. Read the notification and click Reset settings in case you agree
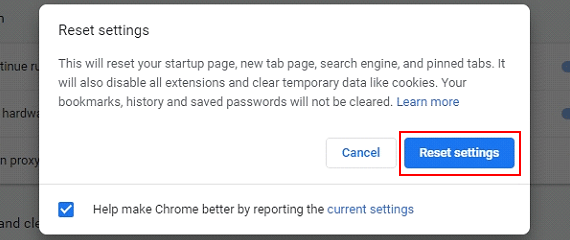
- Restart Chrome.
OnlineVideoConverter ads removal from Mozilla Firefox
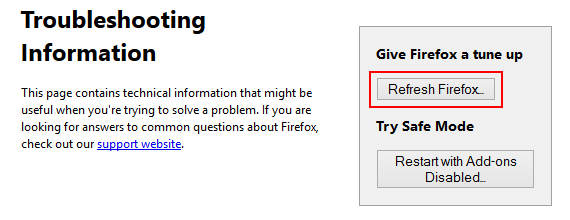
- Open Firefox and select Troubleshooting Information on the Help drop-down list
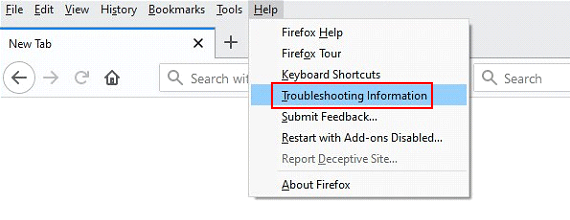
- Locate the sub-section titled Give Firefox a tune up and click on the Refresh Firefox button to proceedLocate the sub-section titled Give Firefox a tune up and click on the Refresh Firefox button to proceed. Then confirm the transaction on the respective popup
- Restart Firefox.
OnlineVideoConverter ads removal from Internet Explorer
- Select Internet Options under Tools in IE
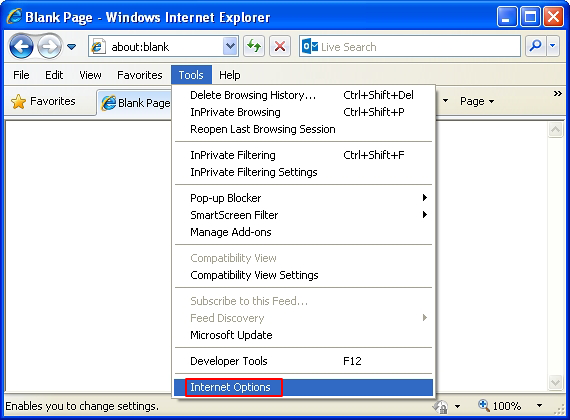
- Select the Advanced tab on Internet Options screen and click on the Reset button
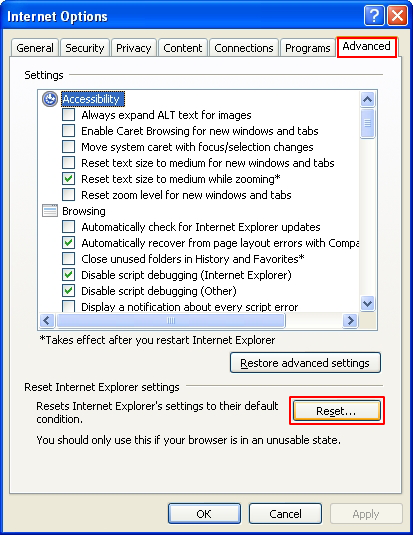
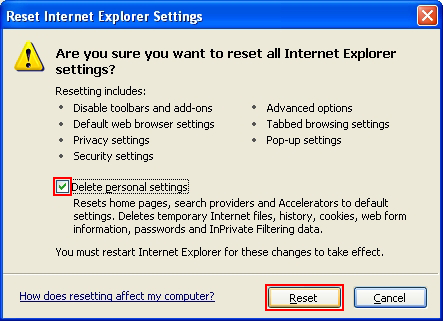
- The browser will now display the Reset Internet Explorer Settings dialog. Review the points on what the resetting includes. Activate the option saying Delete personal settings and click on the Reset button as shown on the image
- Restart the computer.
Verify thoroughness of the removal
Having carried out the instructions above, add a finishing touch to the security procedure by running an additional computer scan to check for residual malware activity.