If you see the Merry_i_love_you_bruce file – it is a confession made by the crooks that they have hacked data for ransom. For that purpose, they have developed a malicious application called Merry X-Mas ransomware. Their product is able to deploy a complex encryption system. The impact is strong enough to withstand any direct intervention. That is, if you apply a straightforward computing power, that will not do. Even if you get the fastest PC in the world, the computations able to produce the private key will take ages.
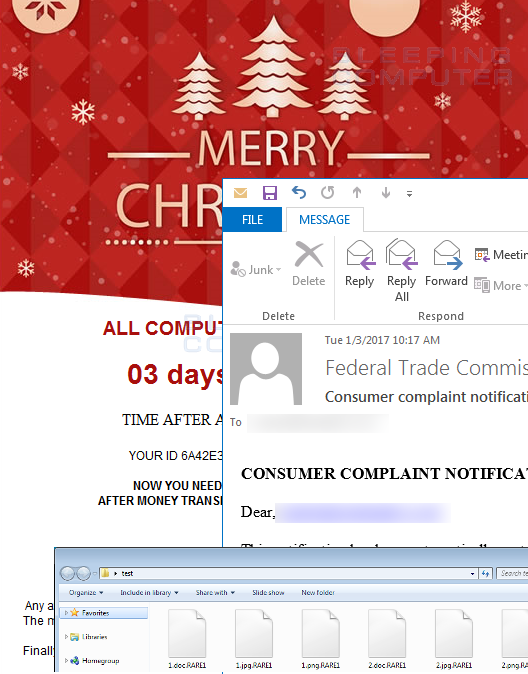
Merry_i_love_you_bruce owes its name to the file denomination that contains a ransom note. The infection, having completed the malicious encryption, creates a file dubbed Merry_i_love_you_bruce.hta which the victims find in each directory with the affected data. Besides, the ransomware drops the same to the desktop. Other versions of Merry X-Mas virus may create .RARE1, .MERRY, .MRCR1 file extensions.
The message may include the picture of Robot Santa from Futurama. That suggests the rogue is closely related to another recently released malware known as Merry X-Mas ransomware.
To get installed on the host machine the rogue resorts to a number of schemes. Spamming and direct introduction from malicious websites both make predominant infecting vectors.
Once installed, the infection rather lingers for a while. It does not proceed with its encryption immediately. The lingering period actually enables the ransomware to collect basic data on the host machine and transfer it to the remote server.
The initial stage is followed by the scan that aims to spare a couple of data formats. This does not mean the ransomware is so kind; it just wants its victims to read the ransom message. The easiest way is to make them read the ransom note right from the device hit by the extortion virus. The users cannot read anything, where the operating system has collapsed. The system inevitably falls where its critical files cannot be rendered. That is the only reason for the Merry X-Mas ransomware to spare certain files and thus exclude some formats from the target.
A contemporary ransomware tends to be interactive. That is not the case with Merry X-Mas virus. It is an old school extortionist that wants its victims to write an individual letter without any template. The mailbox they indicate is often registered with yahoo.com. That suggests the scam originates from Russia.
A victim may write anything, but the only info the scammers are going to process is actually the unique code included in the initial ransom note. The scammer’s feedback indicates the ransom amount to be paid. The sum varies and may be as high as 5 BTC, which is almost 5,000 USD. Paying the ransom demanded shall not be considered a reasonable option. To get rid of the Merry Ransomware and its impacts, kindly proceed with the guidance below.
Automatic removal of Merry X-Mas Ransomware
The benefits of using the automatic security suite to get rid of this infection are obvious: it scans the entire system and detects all potential fragments of the virus, so you are a few mouse clicks away from a complete fix.
- Download and install recommended malware security suite
- Select Start Computer Scan feature and wait until the utility comes up with the scan report. Proceed by clicking on the Fix Threats button, which will trigger a thorough removal process to address all the malware issues compromising your computer and your privacy.
Restore files locked by Merry X-Mas ransomware
Merry X-Mas represents a unique category of malicious software whose attack surface reaches beyond the operating system and its components, which is why removing the virus itself is a part of the fix only. As it has been mentioned, it encrypts one’s personal information, so the next phase of the overall remediation presupposes reinstating the files that will otherwise remain inaccessible.
-
Launch data recovery software
Similarly to the rest of its fellow-infections, Merry X-Mas most likely follows an operational algorithm where it erases the original versions of the victim’s files and actually encrypts their copies. This peculiarity might make your day, because forensics-focused applications like Data Recovery Pro are capable of restoring the information that has been removed. As the virus further evolves, its modus operandi may be altered – in the meanwhile, go ahead and try this.
-
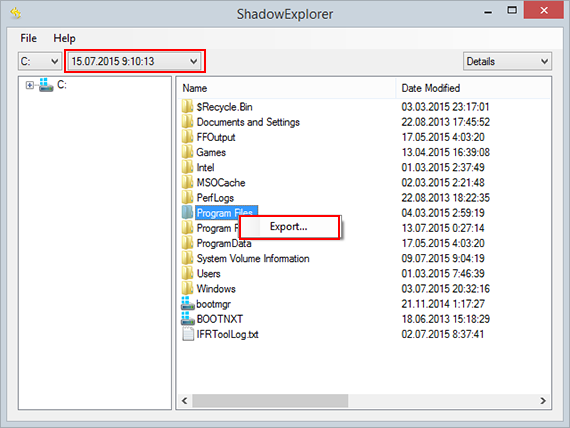
Take advantage of Volume Shadow Copy Service
This technique is based on using the native backup functionality that’s shipped with Windows operating system. Also referred to as Volume Snapshot Service (VSS), this feature makes regular backups of the user’s files and keeps their most recent versions as long as System Restore is on. Merry X-Mas virus hasn’t been found to affect these copies therefore the restoration vector in question is strongly recommended. The two sub-sections below highlight the automatic and manual workflow.
- a) Use Shadow Explorer
Shadow Explorer is an applet that provides an easy way of retrieving previous versions of files and folders. Its pro’s include an intuitive interface where the computer’s entire file hierarchy is displayed within one window. Just pick the hard disk volume, select the object or directory to be restored, right-click on it and choose Export. Follow the app’s prompts to get the job done.
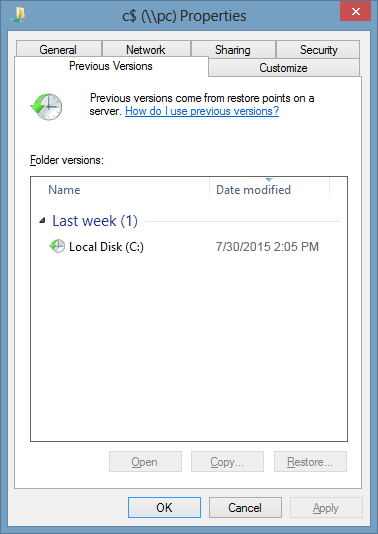
- b) Use file properties
Essentially, what the above-mentioned Shadow Explorer tool does is it automates the process that can otherwise be performed manually via the Properties dialog for individual files. This particular approach is more cumbrous but just as effective as its software-based counterpart, so you can proceed by right-clicking on a specific file, which has been encrypted by Merry X-Mas ransomware, and selecting Properties in the context menu. The tab named Previous Versions is the next thing to click – it displays available versions of the file by date of the snapshot creation. Pick the latest copy and complete the retrieval by following the prompts.
-
Data backups work wonders
Ransomware like Merry X-Mas isn’t nearly as almighty and destructive in case you run regular file backups to the cloud or external data media. The virus itself can be completely removed in a matter of minutes, and the distorted information can then be just as easily recovered from the backup. Luckily, this is a growing trend, so ransom Trojans are hopefully going to become less subversive in the near future.
Verify thoroughness of the removal
Having carried out the instructions above, add a finishing touch to the security procedure by running an additional computer scan to check for residual malware activity