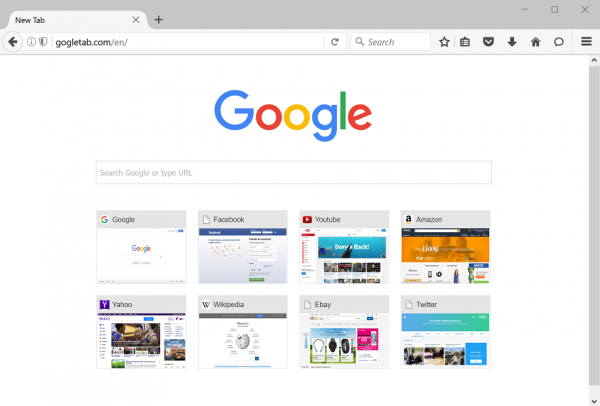
Gogletab.com logs online data. It is not a Google authorized solution. It bears the name that looks like Google to catch the weasel asleep. Unsuspecting users are unaware the actions they take with gogletab get recorded; the records flow to the unverified server. It is not quite clear what is going on afterwards. afterwards. Odds are the follow-up uses of the information on your browsing habits violate your cyber privacy and security.
It is not that Google is a saint and an example of fair play. Its unauthorized imitation is much worse, though.
Our speculation does not answer the main question that troubles the users concerned: how does URL manage to occupy browsers? IT experts commonly define such an occupation a browser hijacking. The URL, or the website itself, does not take over the browser via the online channel. Instead, it has a buggy app that hits browsing software. The program installs using a range of infection vectors. The prevailing method bundles the adware with a third party content. The users actually aim at the latter. They do not expect any other items to go along. However, that exactly is going on.
The adware publishers would (try to) justify such a workflow. They appeal to the user’s agreement granted in the course of the installation. Indeed, there is a special online manager that serves the adware and target content introduction. It asks if the user does not mind the browser add-on background installation. Users typically just want it to complete ASAP and click OK in any window.
The above scenario does not exclude other infection vectors. Similarly, it shall not affect user’s right to get rid of gogletab.com redirects. To remove gogletab.com hijacker, proceed with the steps below. After all, the most popular request about gogletab.com seeks the removal thereof.
Automatic removal of Gogletab.com infection
The benefits of using the automatic security suite to get rid of this infection are obvious: it scans the entire system and detects all potential fragments of the virus, so you are a few mouse clicks away from a complete fix.
- Download and install recommended malware security suite
- Select Start Computer Scan feature and wait until the utility comes up with the scan report. Proceed by clicking on the Fix Threats button, which will trigger a thorough removal process to address all the malware issues compromising your computer and your privacy.
Get rid of Gogletab.com using Windows native uninstall feature
- Select Control Panel entry in the Windows Start menu. Go to Programs and Features (Windows 8), Uninstall a program (Windows Vista / Windows 7) or Add or Remove Programs (Windows XP)
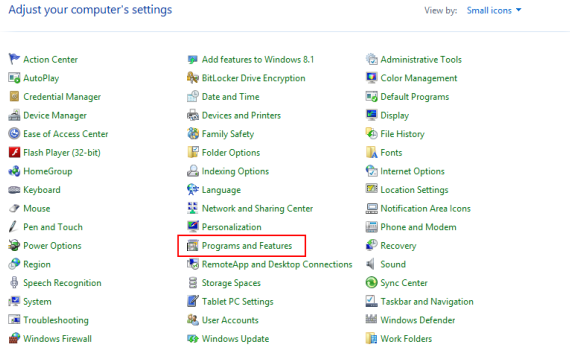
- On the Uninstall or change a program screen, find the entry for Gogletab.com or any similar-looking new application. Select it and click Uninstall/Change
- Be advised this technique works well for the regular applications but might be inefficient for removing malicious programs.
Remove Gogletab.com virus from web browser
The workflow below is intended to eliminate malicious objects, such as add-ons or plugins, from the browsers that got impacted. Given the persistence-related features of this particular infection, the optimal workaround is to restore the affected browser’s settings to their original state. This will prevent the virus from further interfering with your preferences.
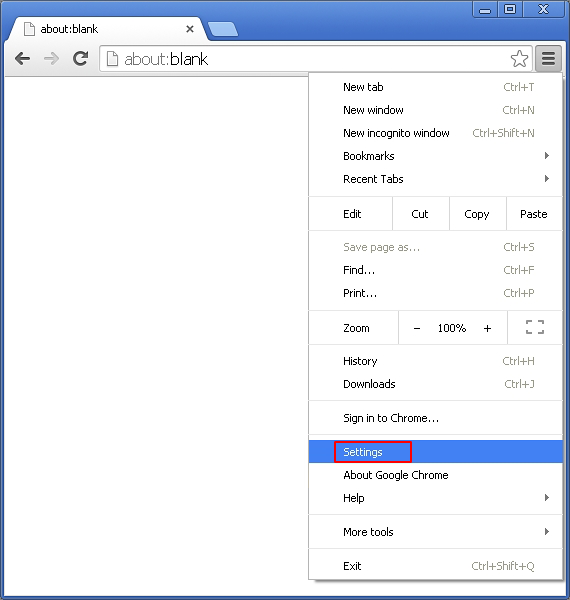
Gogletab.com removal from Google Chrome
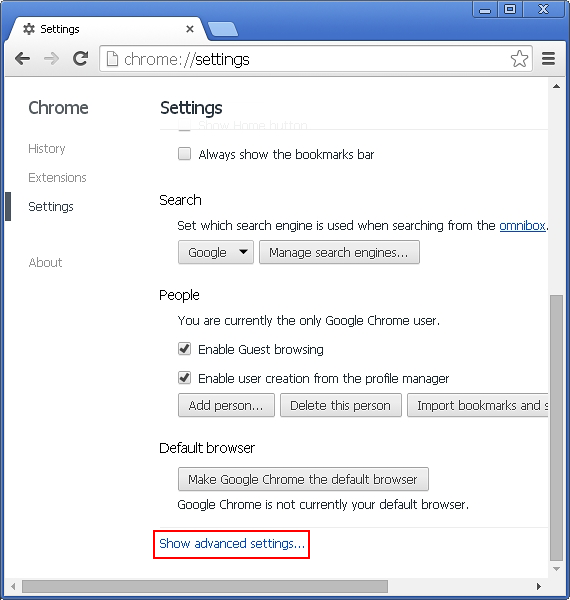
- Click the Chrome menu icon and select Settings
- When the Settings screen opens, find the link that says Show advanced settings and click on it
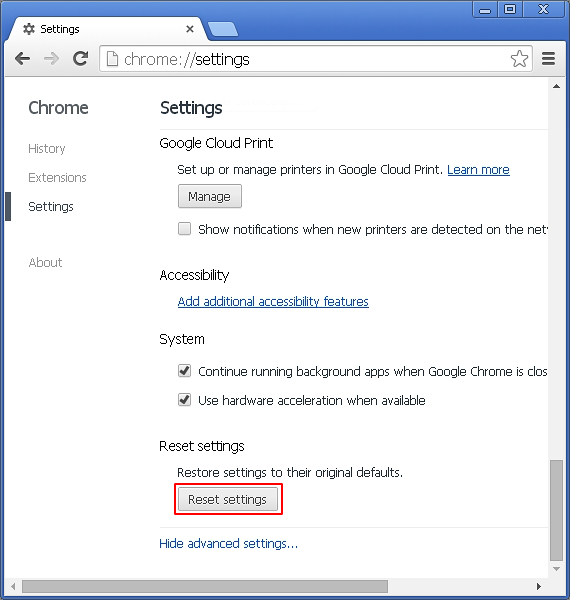
- Proceed by clicking on the Reset browser settings button
- For you to evade any unintended consequences of the reset, Chrome will display a note about the settings and fragments of browsing data that will be lost. Read the notification and click Reset in case you agree
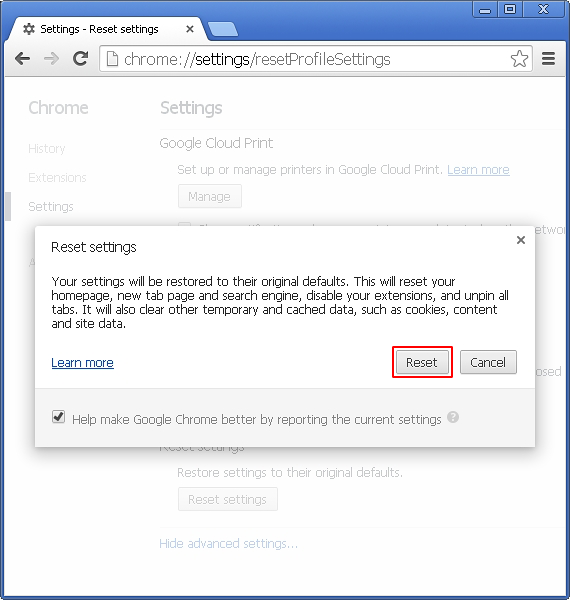
- Restart Chrome.
Gogletab.com removal from Mozilla Firefox
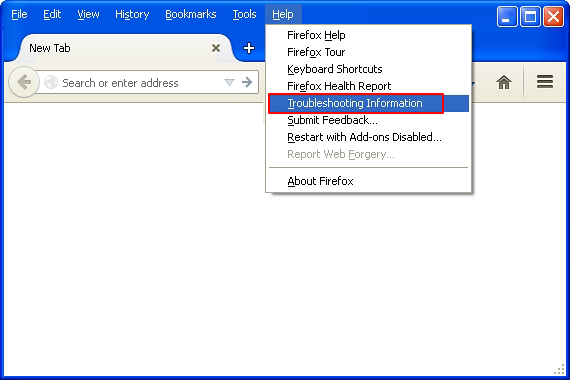
- Open Firefox and select Troubleshooting Information on the Help drop-down list
- Locate the sub-section titled Give Firefox a tune up and click on the Refresh Firefox button to proceed. Then confirm the transaction on the respective popup
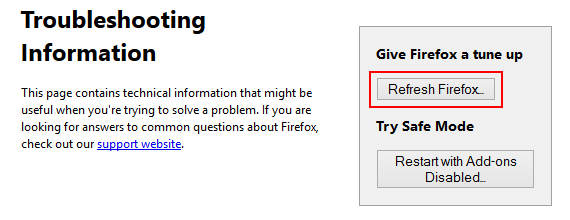
- Restart Firefox.
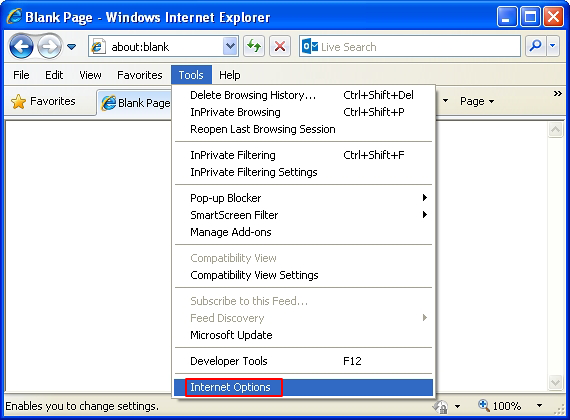
Gogletab.com removal from MS Internet Explorer
- Select Internet Options under Tools in IE
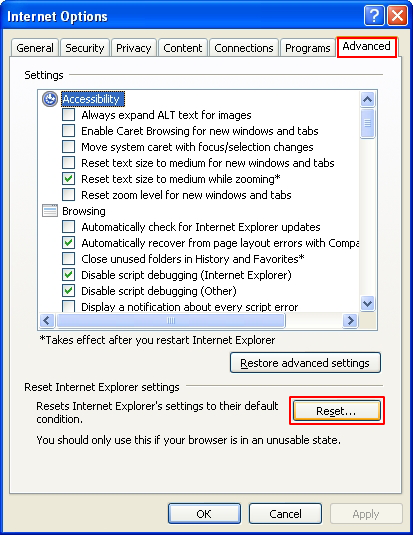
- Select the Advanced tab on Internet Options screen and click on the Reset button
- The browser will now display the Reset Internet Explorer Settings dialog. Review the points on what the resetting includes. Activate the option saying Delete personal settings and click on the Reset button as shown on the image
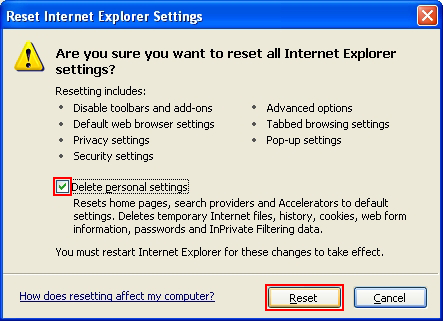
- Restart the computer
Verify thoroughness of the removal
Having carried out the instructions above, add a finishing touch to the security procedure by running an additional computer scan to check for residual malware activity.