MTview.exe search hijacker aims at the requests to your expected search engine. The engine could be Google or any other one you favor. In case there are no such preferences, the invader simply nominates itself as your default.
The procedure of redirecting you to the search page is powered by special application. It is deemed to be a search hijacker. That is because it actually hijacks relevant browser settings.
The MTview application often installs its components via third party download routine. The installation typically goes as follows.
A user opts for grabbing certain free items from the Internet storage. This could be any media player, image handling software etc. To get the desired attempts, the user is to launch a download. That basically requires one to click a link. The click triggers a download manager interface. The user is requested to click several buttons. The buttons refer to user agreement for the installation under such and such conditions.
That sounds like a standard procedure. However, if you accept all the conditions in bulk, the hijacker installs along with the target items. Formally, you have agreed its introduction as you have loaded the primary contents.
The hijacker is often referred to as a secondary content. That is because it is installed at the background of the primary items.
It is good to take a precaution as you grab free stuff out of the worldwide web. On the other hand, the distributors of the hijacker obviously play hoax with us. They are well-aware that very few are to verify what they get free of charge.
Besides, the makers of MTview.exe intentionally aggravates its removal. Uninstalling does not remove MTview.exe virus.
Few users thus install the adware deliberately. Therefore, it is deemed to hack computers and hijack their browsers.
The installation modifies settings of all the browsers installed on affected computers. The infection, in particular, sets its favored page to load as a new tab, start page.
The most important vector of the attack is the search engine. The MTview.exe hijacker makes its best to ensure you do not have access to your favorite engine. The restriction may be complete or partial.
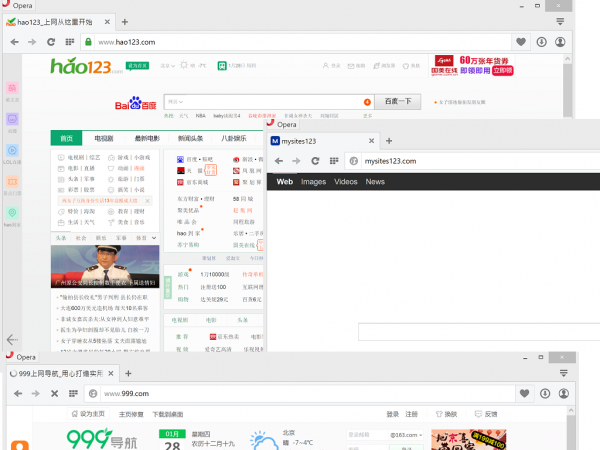
In the case of partial restriction, the user is forced to visit the rogue page prior to the requested the desired engine. The infection typically does not allow direct access to the search pages. Besides, it may allow access through its own page to a single engine only like 999.com or Hao123com, etc.
A partial restriction may block the access to any search engine. Instead of the page requested, be it Google or Yahoo, MTview.exe loads its own one. However, any search query made with the page sponsored by the hijacker is eventually processed by Google. The rogue may only slightly modify the returned links with its commercials. Any other engines but Google are not available in the above case.
The above is but an example. The hijacker may as well block any search engines but Yahoo, any but Bing etc. The behavior varies from case to case.
Regardless of the invasion conditions and follow-up behavior, the removal of MTview.exe search hijacker is a prerequisite of proper web-navigation. To get rid of MTview.exe redirects, apply elaborate removal guidance.
Automatic removal of MTview.exe infection
The benefits of using the automatic security suite to get rid of this infection are obvious: it scans the entire system and detects all potential fragments of the virus, so you are a few mouse clicks away from a complete fix.
- Download and install recommended malware security suite
- Select Start Computer Scan feature and wait until the utility comes up with the scan report. Proceed by clicking on the Fix Threats button, which will trigger a thorough removal process to address all the malware issues compromising your computer and your privacy.
Get rid of MTview.exe using Windows native uninstall feature
- Select Control Panel entry in the Windows Start menu. Go to Programs and Features (Windows 8), Uninstall a program (Windows Vista / Windows 7) or Add or Remove Programs (Windows XP)
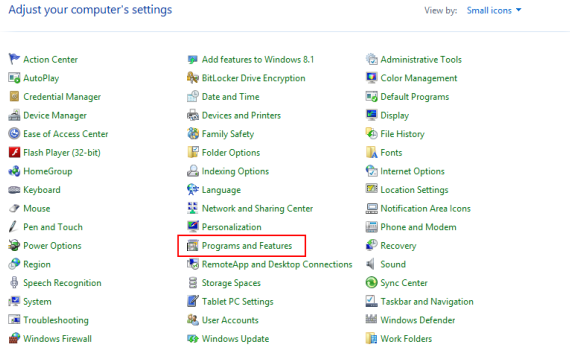
- On the Uninstall or change a program screen, find the entry for MTview or any similar-looking new application. Select it and click Uninstall/Change
- Be advised this technique works well for the regular applications but might be inefficient for removing malicious programs.
Remove MTview.exe virus from web browsers
The workflow below is intended to eliminate malicious objects, such as add-ons or plugins, from the browsers that got impacted. Given the persistence-related features of this particular infection, the optimal workaround is to restore the affected browser’s settings to their original state. This will prevent the virus from further interfering with your preferences.
MTview.exe removal from Google Chrome
- Click the Chrome menu icon and select Settings
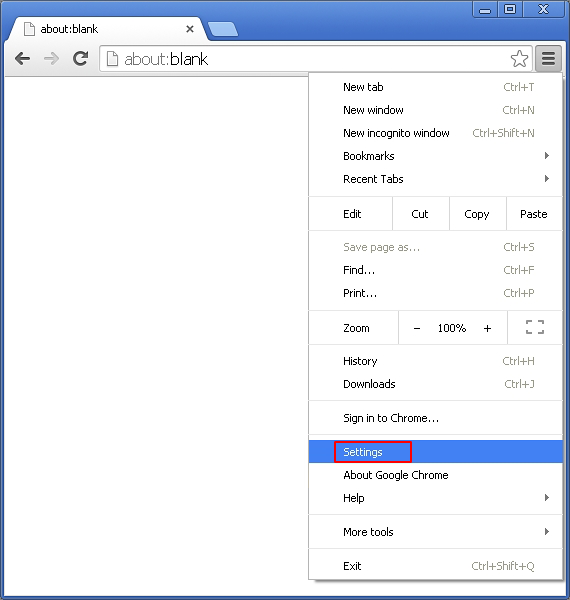
- When the Settings screen opens, find the link that says Show advanced settings and click on it
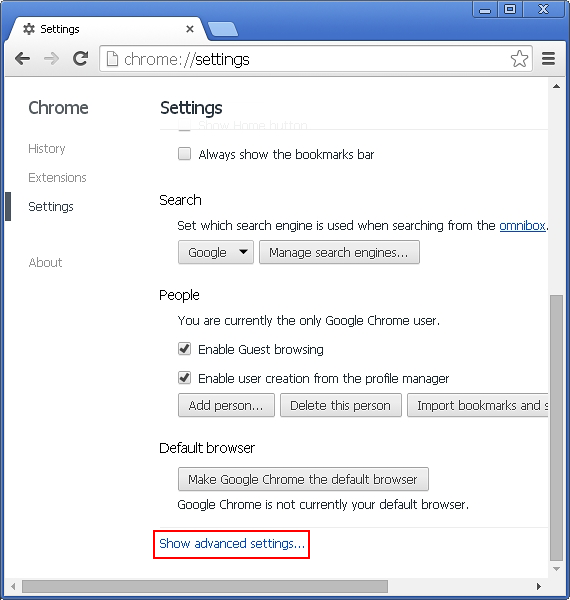
- Proceed by clicking on the Reset browser settings button
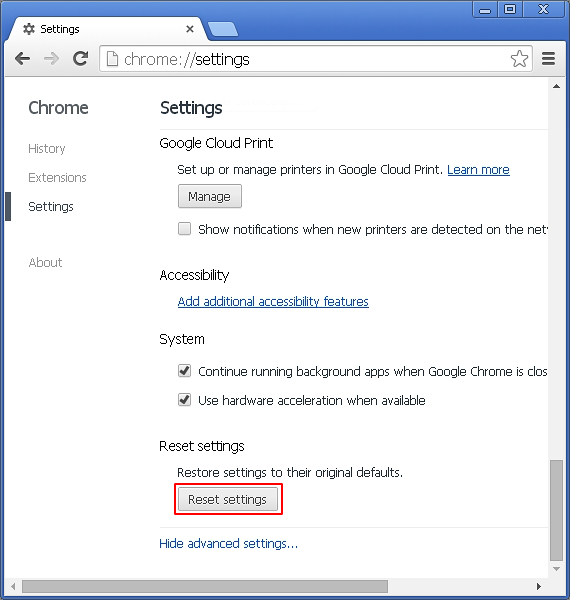
- For you to evade any unintended consequences of the reset, Chrome will display a note about the settings and fragments of browsing data that will be lost. Read the notification and click Reset in case you agree
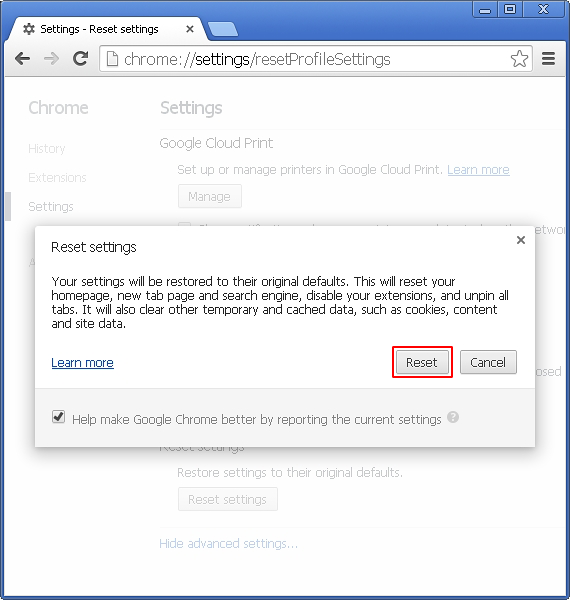
- Restart Chrome.
MTview.exe removal from Mozilla Firefox
- Open Firefox and select Troubleshooting Information on the Help drop-down list
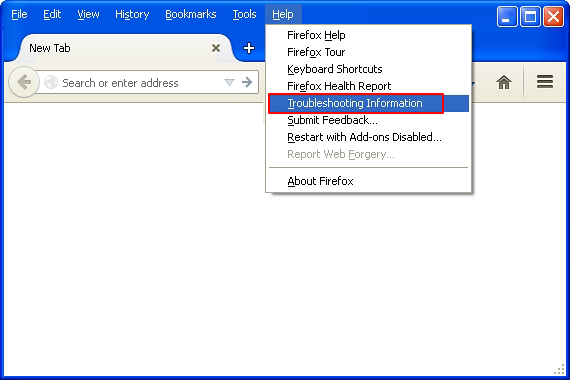
- Locate the sub-section titled Give Firefox a tune up and click on the Refresh Firefox button to proceed. Then confirm the transaction on the respective popup
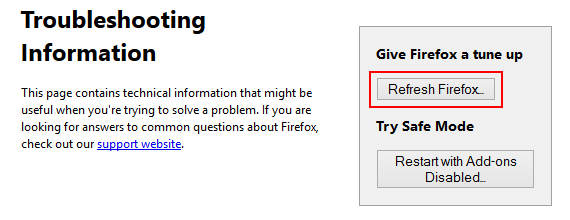
- Restart Firefox.
MTview.exe removal from MS Internet Explorer
- Select Internet Options under Tools in IE
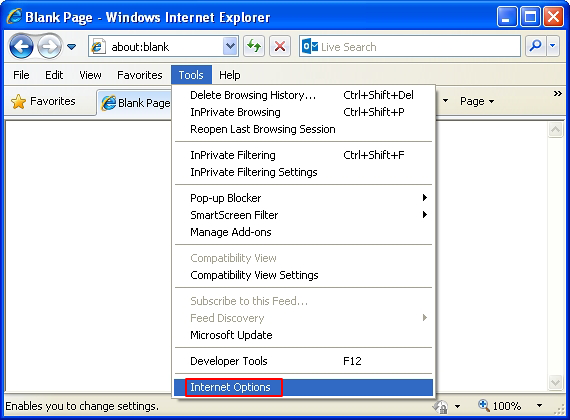
- Select the Advanced tab on Internet Options screen and click on the Reset button
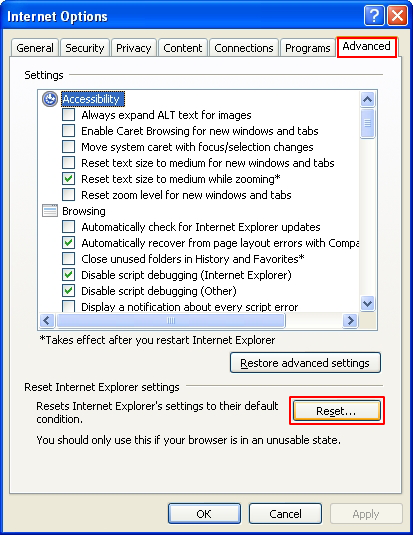
- The browser will now display the Reset Internet Explorer Settings dialog. Review the points on what the resetting includes. Activate the option saying Delete personal settings and click on the Reset button as shown on the image
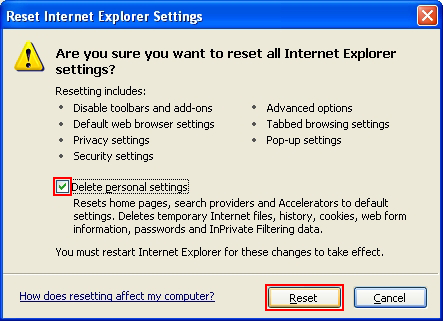
- Restart the computer
Verify thoroughness of the removal
Having carried out the instructions above, add a finishing touch to the security procedure by running an additional computer scan to check for residual malware activity.