Most ransomware campaigns are geographically scattered to maximize their reach. While this is an understandable tactic of the extortionists, some blackmail infections target specific areas only. This is the case with GermanWiper, a ransom Trojan that splashed onto the cybercrime scene in early August 2019. It was denominated this way by researchers who discovered the malicious code. Obviously, the audience of its victims spans users and organizations located in Germany, with no other countries being affected at this point. Those who got hit, though, refer to the pest based on the symptoms that it causes rather than the term coined by analysts. One of telltale signs of the raid is the ransom note named Entschluesselungs_Anleitung.html (German for “Decryption Instructions”) prepended by a unique extension string assigned to each plagued user individually.
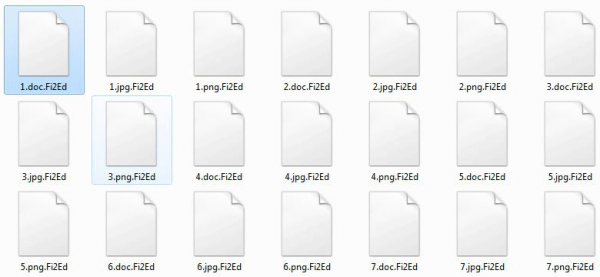
One more indicator of the attack is the extension concatenated to all important files belonging to the victim. It consists of five alphanumeric characters. For instance, an arbitrary Word document Glossary.docx will turn into something like Glossary.docx.0mkL3. By the way, this random tail matches the prefix in the name of the ransom note mentioned above. In this hypothetical scenario, the crooks’ recovery manual dropped onto a computer will be 0mkL3_Entschluesselungs_Anleitung.html. The GermanWiper ransomware additionally replaces the desktop wallpaper image with a warning message that says,
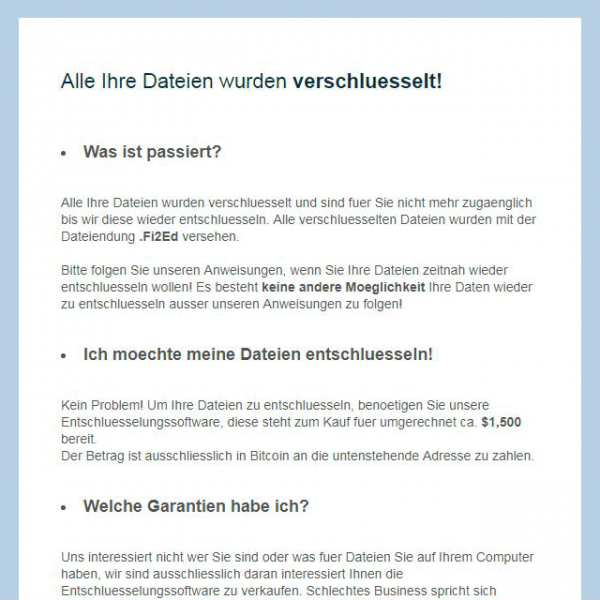
Ihre Dateien wurden verschluesselt. Oeffnen Sie [ransom note name] um herauszufinden wie Sie Ihre Dateien entschluesseln koennen!
This inscription coerces the user to open the rescue document and follow the embedded instructions.
The ransom Trojan demands about $1,500 worth of Bitcoin for the data recovery. To be more precise, the amount is 0.15 BTC and the fiat currency equivalent depends on the current rate. The receiving cryptocurrency wallet address varies from case to case, which is probably an attempt to throw the law enforcement off the trail. In return for the payment, the cybercriminals claim to provide a tool with a built-in decryption key that will supposedly reinstate all the twisted records.
However, there is a huge caveat in this regard. According to researchers’ preliminary takeaways stemming from the analysis of GermanWiper virus in its present-day state, the files are simply overwritten rather than encoded. It means that there might be no viable recovery mechanism even if the ransom is paid. This is definitely bad news for the victims, but it’s quite possible that the malefactors will fix the glitch in their code sometime soon and release another variant of the culprit. Otherwise, they won’t be making any dirty money once the complete lack of decryption option gains publicity.
GermanWiper is doing the rounds through phishing. The would-be preys receive a message camouflaged as a female job applicant’s CV. The attached ZIP archive, when extracted, appears to include two PDF files. However, these objects turn out to be LNK entities in disguise, which run a covert PowerShell script. The script then downloads another file in HTA format that pulls in and executes the final-stage payload. The ransomware executable proper is dropped into the Public directory under C:\Users. The next stage of the attack is to scan the host for valuable data. When doing its checks, the ransomware skips system paths that are critical for normal operation of Windows. The weirdest part comes next: GermanWiper overwrites the contents of spotted important files with zeroes, making it both inaccessible and irrecoverable. Again, this may be a flaw in the malware code that the attackers are likely to rectify in a future update of the infection. Therefore, the following steps are worth trying anyway to restore the hostage information. Furthermore, the virus removal part is a must regardless of the ransomware variant.
Automatic removal of GermanWiper ransomware
The benefits of using the automatic security suite to get rid of this infection are obvious: it scans the entire system and detects all potential fragments of the virus, so you are a few mouse clicks away from a complete fix.
- Download and install recommended malware security suite
- Select Start Computer Scan feature and wait until the utility comes up with the scan report. Proceed by clicking on the Fix Threats button, which will trigger a thorough removal process to address all the malware issues compromising your computer and your privacy.
Restore files locked by GermanWiper
The GermanWiper ransomware represents a unique category of malicious software whose attack surface reaches beyond the operating system and its components, which is why removing the virus itself is a part of the fix only. As it has been mentioned, it encrypts one’s personal information, so the next phase of the overall remediation presupposes reinstating the files that will otherwise remain inaccessible.
-
Launch data recovery software
Similarly to the rest of its fellow-infections, the GermanWiper virus most likely follows an operational algorithm where it erases the original versions of the victim’s files and actually encrypts their copies. This peculiarity might make your day, because forensics-focused applications like Data Recovery Pro are capable of restoring the information that has been removed. As the virus further evolves, its modus operandi may be altered – in the meanwhile, go ahead and try this.
-
Take advantage of Volume Shadow Copy Service
This technique is based on using the native backup functionality that’s shipped with Windows operating system. Also referred to as Volume Snapshot Service (VSS), this feature makes regular backups of the user’s files and keeps their most recent versions as long as System Restore is on. GermanWiper hasn’t been found to affect these copies therefore the restoration vector in question is strongly recommended. The two sub-sections below highlight the automatic and manual workflow.
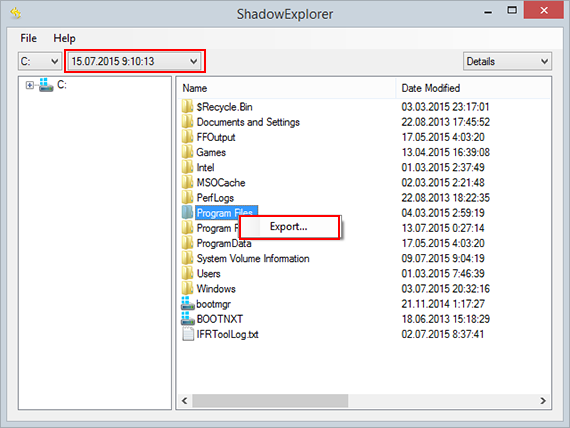
- a) Use Shadow Explorer
Shadow Explorer is an applet that provides an easy way of retrieving previous versions of files and folders. Its pro’s include an intuitive interface where the computer’s entire file hierarchy is displayed within one window. Just pick the hard disk volume, select the object or directory to be restored, right-click on it and choose Export. Follow the app’s prompts to get the job done.
- b) Use file properties
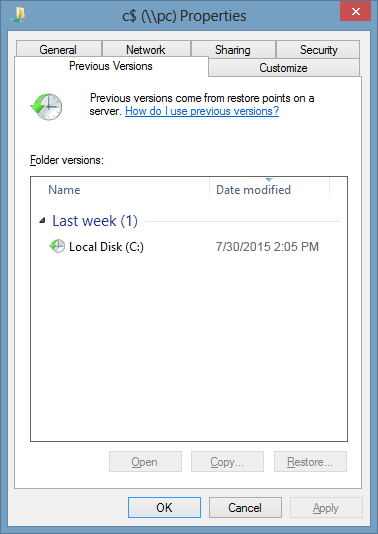
Essentially, what the above-mentioned Shadow Explorer tool does is it automates the process that can otherwise be performed manually via the Properties dialog for individual files. This particular approach is more cumbrous but just as effective as its software-based counterpart, so you can proceed by right-clicking on an arbitrary file with a five-character extension, which has been affected by GermanWiper ransomware, and selecting Properties in the context menu. The tab named Previous Versions is the next thing to click – it displays available versions of the file by date of the snapshot creation. Pick the latest copy and complete the retrieval by following the prompts.
-
Data backups work wonders
Ransomware like GermanWiper isn’t nearly as almighty and destructive in case you run regular file backups to the cloud or external data media. The virus itself can be completely removed in a matter of minutes, and the distorted information can then be just as easily recovered from the backup. Luckily, this is a growing trend, so ransom Trojans are hopefully going to become less subversive in the near future.
Verify thoroughness of the removal
Having carried out the instructions above, add a finishing touch to the security procedure by running an additional computer scan to check for residual malware activity