StorageCrypt ransomware targets cloud and other network attached storage (NAS) devices as its distributors make use of SambaCry vulnerability to drop the infection. The vulnerability is also known to be exploited for unauthorized installation of cryptocurrency miners. Basically, SambaCry is a flaw that occurs as you create a remote network drive using Samba software. The hackers are able to remotely access the drive. They at least can download files and execute commands on the hacked devices.
It is not quite clear whether the hackers introduce StorageCrypt ransomware directly or via a backdoor. Meanwhile, the attack actually drops a trojan called sambacry. When stored, the file is renamed to apaceha and located at /tmp folder. Perhaps, this is the backdoor that finally drops StorageCrypt ransomware.
This way or another, SambaCry vulnerability results in the ransomware installation. The infection applies a mix of RSA and AES ciphers to scramble the data under attack. Each of the methods applied is strong enough to withstand any feasible decryption-by-computation attempts. The files hacked by the malicious encryptor get their names modified as the .locked extension is added to the original filename.
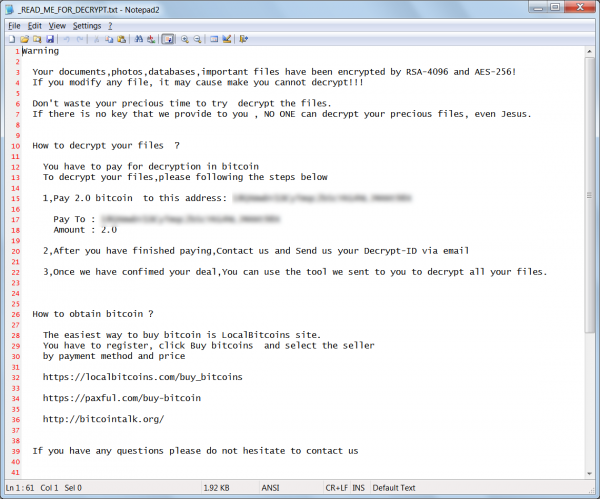
_READ_ME_FOR_DECRYPT.txt is the file that contains the message of the attackers. They claim the ransom amounted to 0.4 to 2 bitcoins. The notification also specifies the bitcoin wallet for relevant transfer.
StorageCrypt ransomware invasion via SambaCry also creates Autorun.inf and 美女与野兽.exe files in each folder of the NAS. ‘美女与野兽’ translates to ‘The Beauty and the Beast’. The pair of files aims at propagating the ransomware further to any computer that communicates with the compromised NAS. The response to the malware invasion, apart from the data recovery, shall encompass the removal of those related threats. To this end, a detailed guidance on the removal of StorageCrypt encryption-for-ransom is available below.
Automatic removal of StorageCrypt Virus
The benefits of using the automatic security suite to get rid of this infection are obvious: it scans the entire system and detects all potential fragments of the virus, so you are a few mouse clicks away from a complete fix.
- Download and install recommended malware security suite
- Select Start Computer Scan feature and wait until the utility comes up with the scan report. Proceed by clicking on the Fix Threats button, which will trigger a thorough removal process to address all the malware issues compromising your computer and your privacy.
Restore files locked by StorageCrypt Virus
new Locky variant aka StorageCrypt Virus represents a unique category of malicious software whose attack surface reaches beyond the operating system and its components, which is why removing the virus itself is a part of the fix only. As it has been mentioned, it encrypts one’s personal information, so the next phase of the overall remediation presupposes reinstating the files that will otherwise remain inaccessible.
-
Launch data recovery software
Similarly to the rest of its fellow-infections, StorageCrypt Virus most likely follows an operational algorithm where it erases the original versions of the victim’s files and actually encrypts their copies. This peculiarity might make your day, because forensics-focused applications like Data Recovery Pro are capable of restoring the information that has been removed. As the virus further evolves, its modus operandi may be altered – in the meanwhile, go ahead and try this.
-
Take advantage of Volume Shadow Copy Service
This technique is based on using the native backup functionality that’s shipped with Windows operating system. Also referred to as Volume Snapshot Service (VSS), this feature makes regular backups of the user’s files and keeps their most recent versions as long as System Restore is on. StorageCrypt Virus ransomware hasn’t been found to affect these copies therefore the restoration vector in question is strongly recommended. The two sub-sections below highlight the automatic and manual workflow.
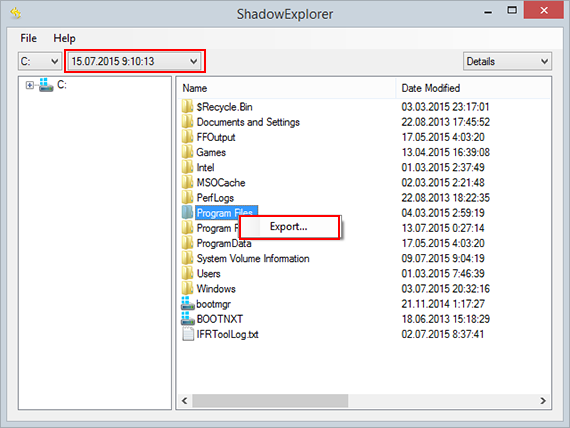
- a) Use Shadow Explorer
Shadow Explorer is an applet that provides an easy way of retrieving previous versions of files and folders. Its pro’s include an intuitive interface where the computer’s entire file hierarchy is displayed within one window. Just pick the hard disk volume, select the object or directory to be restored, right-click on it and choose Export. Follow the app’s prompts to get the job done.
- b) Use file properties
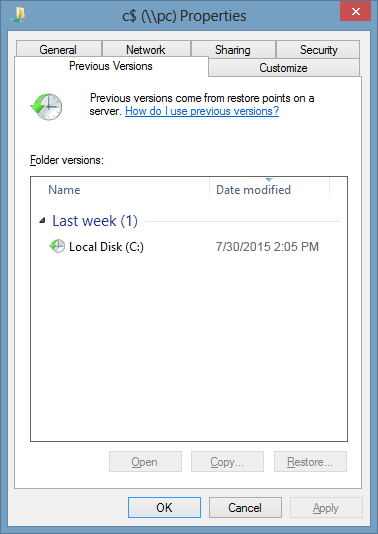
Essentially, what the above-mentioned Shadow Explorer tool does is it automates the process that can otherwise be performed manually via the Properties dialog for individual files. This particular approach is more cumbrous but just as effective as its software-based counterpart, so you can proceed by right-clicking on a specific file, which has been encrypted by StorageCrypt Virus, and selecting Properties in the context menu. The tab named Previous Versions is the next thing to click – it displays available versions of the file by date of the snapshot creation. Pick the latest copy and complete the retrieval by following the prompts.
-
Data backups work wonders
Ransomware like StorageCrypt Virus isn’t nearly as almighty and destructive in case you run regular file backups to the cloud or external data media. The virus itself can be completely removed in a matter of minutes, and the distorted information can then be just as easily recovered from the backup. Luckily, this is a growing trend, so ransom Trojans are hopefully going to become less subversive in the near future.
Verify thoroughness of the removal
Having carried out the instructions above, add a finishing touch to the security procedure by running an additional computer scan to check for residual malware activity